From Invisible to Invincible Stealth-Driven Preemptive Security
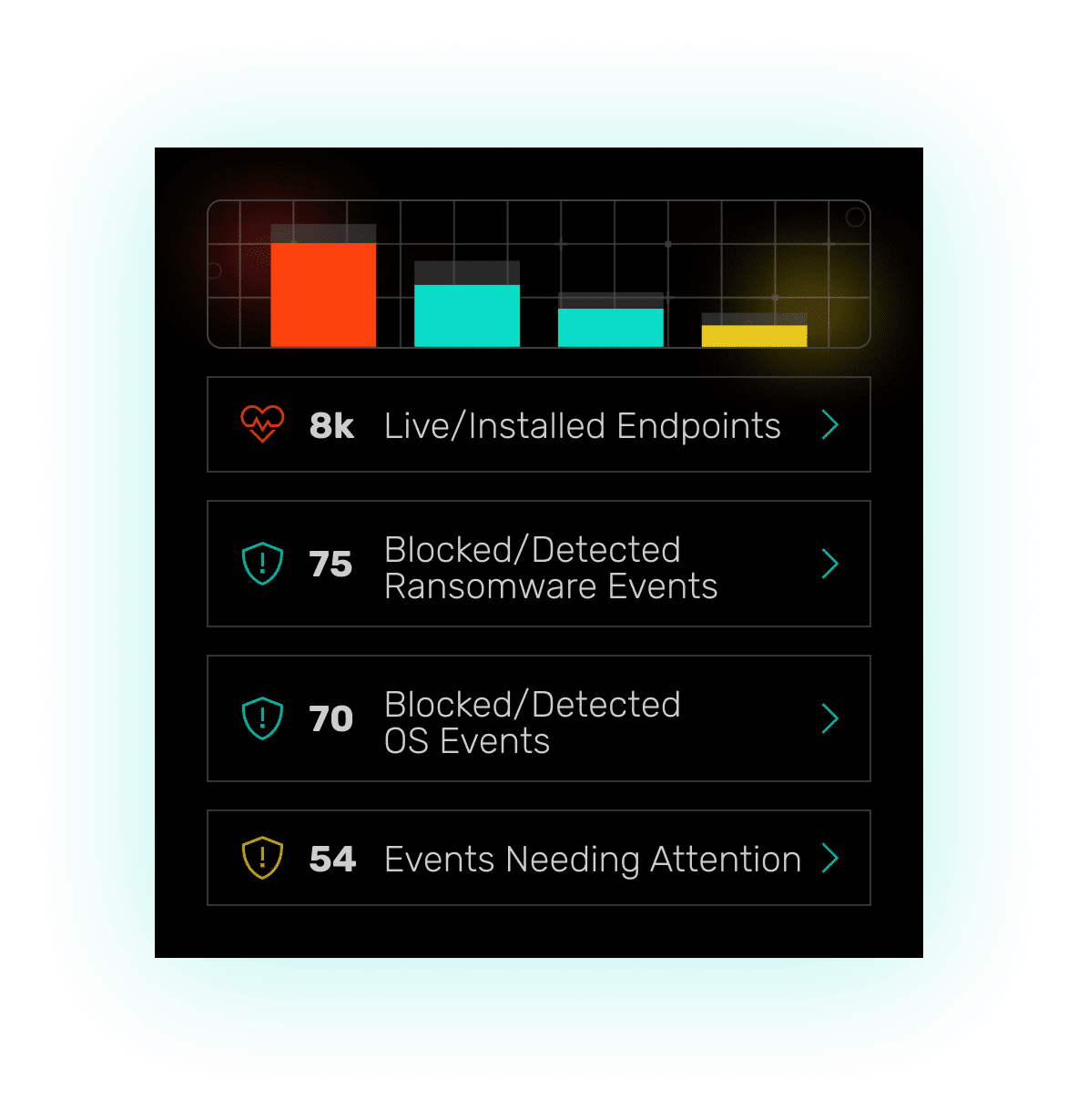
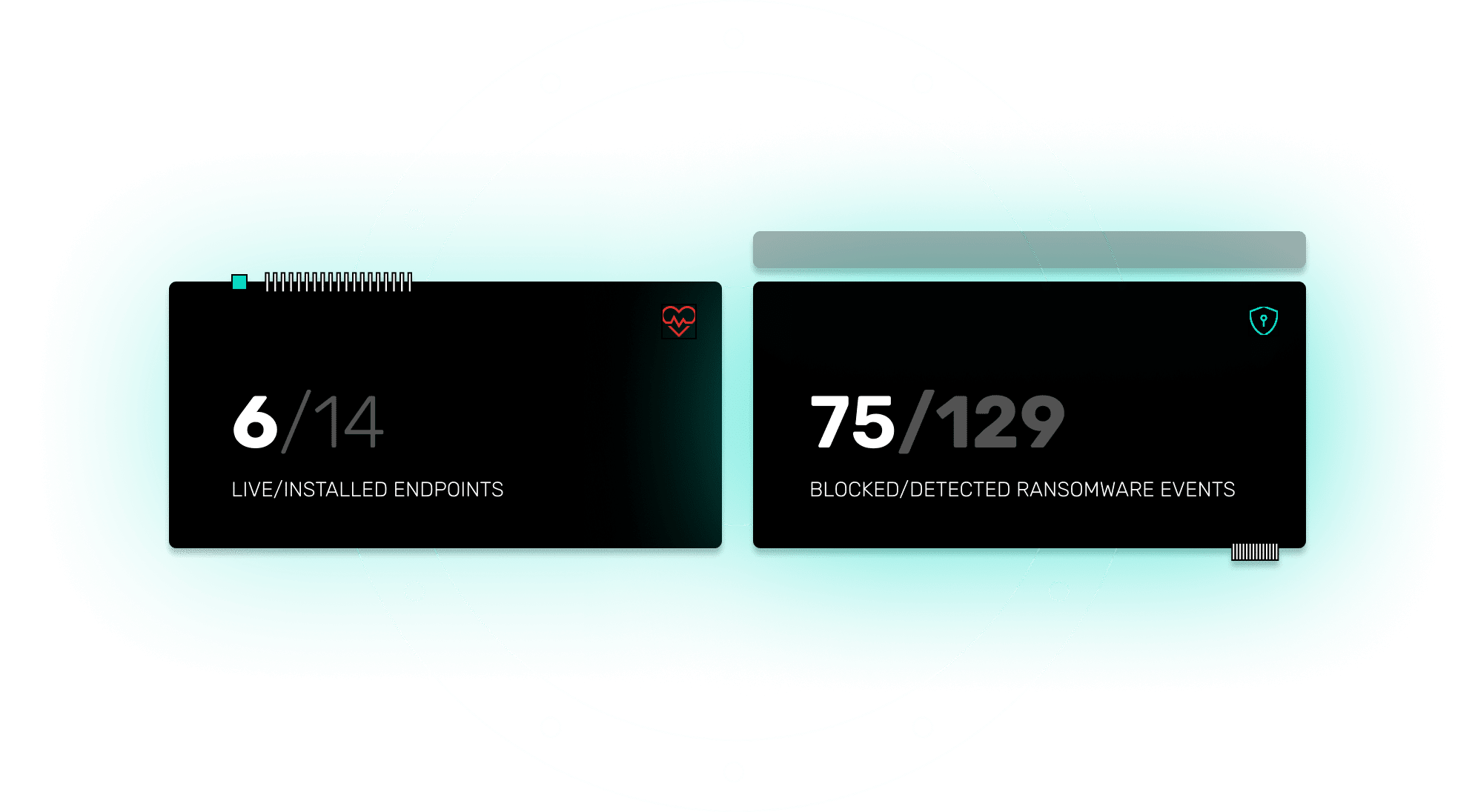
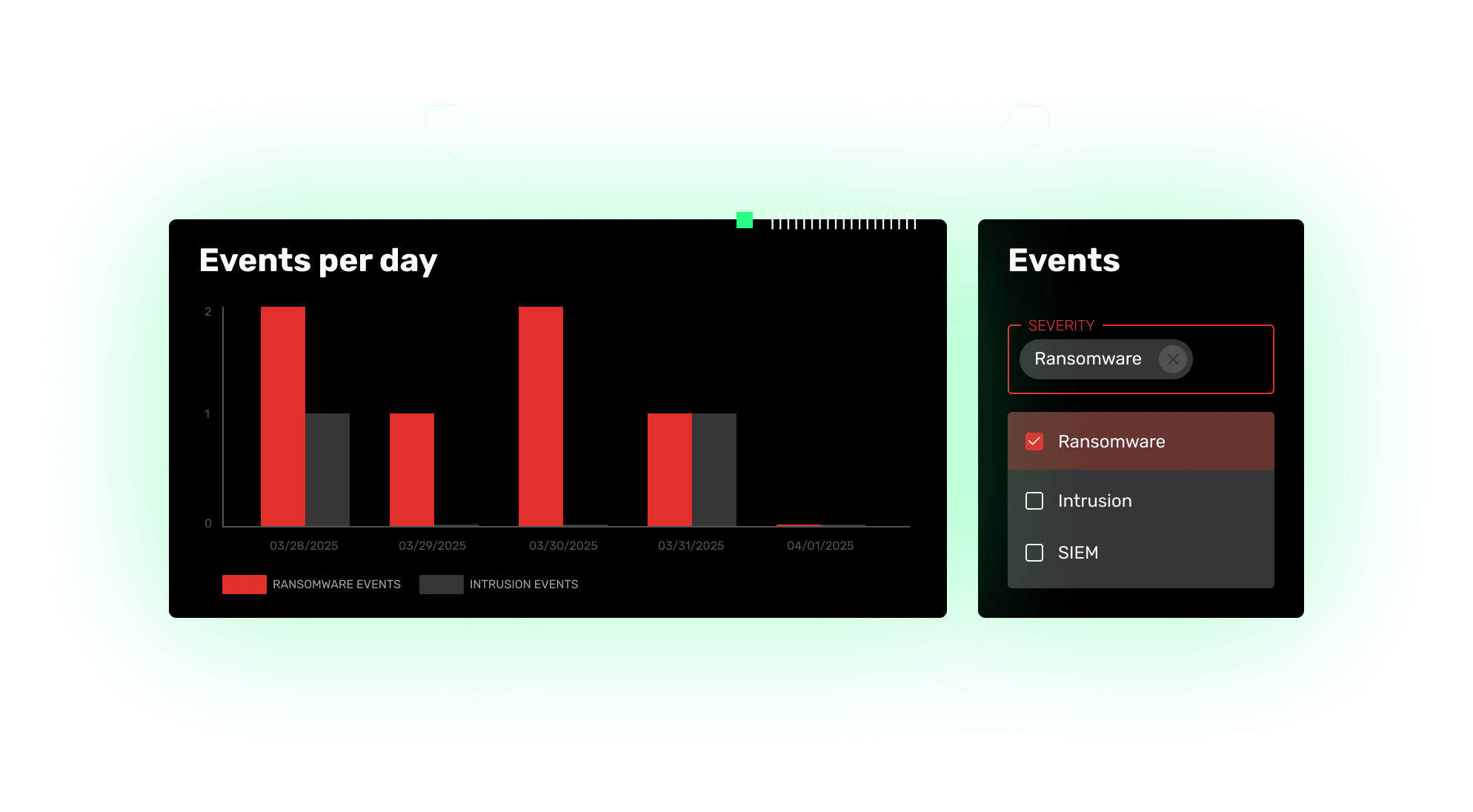
Arms Cyber makes threats irrelevant by keeping your critical data invisible, stopping attacks before they spread, and ensuring no ransom payments, no public breaches, and no business disruption.